What is malware? A dictionary-like definition is “malicious software that attacks computers, smartphones, and other connected devices.”
In fact, “malware” is a mash-up of “malicious software.” It describes any type of software or code specifically designed to exploit a connected device or network without consent. And, unsurprisingly, hackers design most of it for financial gain.
What kinds of malware are there?
Think of malware as an umbrella term that covers an entire host of “bad stuff,” such as:
Spyware that tracks activity, like what you type and where you type it. (Think snooping on your bank account logins.
Ransomware that holds devices or the data on them hostage, that hackers only release for a price. (And even so, payment is no guarantee you’ll get back your access.)
Adware that serves up spammy ads on your device. (The hacker gets paid for the number of “impressions” the ads have. The more they show up on people’s devices, the more they get paid.)
Botnet software, that hijacks a device into a remote-controlled network of other devices. (These networks are used to shut down websites or even shut down large portions of the internet, just to mention two of the things they can do.)
Rootkit that attacks that give hackers remote-control access to a device. (And with that control, they can wage all manner of attacks — on the device and on other devices too.)
Viruses that modify the way a device and its apps function. Also, they can effectively bring a device or network to a grinding halt. (Yes, viruses are a subset of malware. They can copy, delete, and steal data, among other things.)
Viruses, the original malware
You might know malware by its more commonly used name — viruses.
There’s a pretty good reason why people commonly refer to malware as a “virus.” Viruses have been on our collective minds for some time.
Viruses have a long history. You could call it “the original malware.” And depending on how you define what a virus is, the first one took root in 1971 — more than 50 years ago. It was known as Creeper, and rather than being malicious in nature, the creator designed it to show how a self-replicating program could spot other devices on a network, transfer itself to them, and find yet more devices to repeat the process. Later, the same programmer who created a refined version of Creeper developed Reaper, a program that could remove the Creeper program. In a way, Reaper could be considered the first piece of antivirus software.[i]
From there, it wasn’t until the 1980s that malware started affecting the broader population, a time when computers became more commonplace in businesses and people’s homes.
At first, malware typically spread by infected floppy disks, much like the “Brain” virus in 1986. While recognized today as the first large-scale computer virus, its authors say they never intended it to work that way. Rather, they say they created Brain as an anti-piracy measure to protect their proprietary software from theft. However, Brain got loose. It went beyond their software and affected computers worldwide. Although not malicious or destructive in nature, Brain most certainly put the industry, businesses, and consumers on notice. Computer viruses were a thing.[ii]
Another piece of malware that got passed along via floppy disks was the “PC Cyborg” attack that targeted the medical research community in and around 1989. There, the malware would lie in wait until the user rebooted their computer for the 90th time and was presented with a digital ransom note.[iii]
An early example of ransomware – Source, Wikipedia
Upon that 90th boot, PC Cyborg encrypted the computer’s files, which would only get unencrypted if the victim paid a fee, making it the first documented form of ransomware.
Shortly thereafter, the internet started connecting computers, which opened millions of doors for hackers as people went online. Among the most noteworthy was 1999’s “Melissa” virus, which spread by way of infected email attachments and overloaded hundreds of corporate and governmental email servers worldwide.
It was quickly followed in 2000 by what’s considered among the most damaging malware to date — ILOVEYOU, which also spread by way of an attachment, this one posing as a love letter. Specifically, it was a self-replicating worm that installed itself on the victim’s computer where it destroyed some info and stole other info, then spread to other computers. One estimate put the global cost of ILOVEYOU at $10 billion. It further speculated that it infected 10% of the world’s internet-connected computers at the time.[iv]
Antivirus, your best defense against malware
With that history, it’s no surprise that anti-malware software is commonly called “antivirus.”
Antivirus forms a major cornerstone of online protection software. It protects your devices against malware through a combination of prevention, detection, and removal. Our antivirus uses AI to detect the absolute latest threats — and has for several years now.
Today, McAfee registers more than a million new malicious programs and potentially unwanted apps (PUA) each day, which contributes to the millions and millions already in existence. Now with the arrival of AI-powered coding tools, hackers can create new strains at rates unseen before.
That’s another reason why we use AI in our antivirus software. We use AI to protect against AI-created malware. It does so in three ways:
- It detects threats by referencing models of existing threats. This combats pre-existing threats and entirely new (zero-day) threats alike. AI can spot a variety of different threats by comparing them to features it’s seen before. For example, it’s like AI learning to identify different varieties of fruit. An apple is still an apple whether it’s a Fuji or Granny Smith. In that way, a virus is still a virus if it’s “Virus A” or the newly discovered “Virus Z.”
- It further detects unusual events and behaviors. AI provides a particularly powerful tool against zero-day threats. It analyzes the activities of applications for patterns that are consistent with malicious behavior. With that, it can spot and prevent a previously unknown file or process from doing harm. In its way, AI says, “I’ve seen this sketchy behavior before. I’m going to flag it.”
- It automatically classifies threats and adds them to its body of knowledge. AI-driven threat protection gets stronger over time. Because it learns. Something we call “threat intelligence.” The more threats it encounters, the more rapidly and readily it can determine if files want to do you no good. The body of threat intelligence improves immensely as a result.
Once again, it’s important to remind ourselves that today’s malware is created largely for profit. Hackers use it to gain personal and financial info, either for their own purposes or to sell it for profit. The files you have stored on your devices have a street value. That includes tax returns, financial docs, payment info, and so on. Moreover, when you consider all the important things you keep on your devices, like your photos and documents, those have value too. Should you get caught up in a ransomware attack, a hacker puts a price tag on them for their return.
Needless to say, and you likely know this already, antivirus is essential for you and your devices.
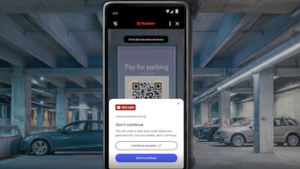
You’ll find our AI-powered antivirus in all our McAfee+ plans. Better yet, our plans have dozens of protections that block the ways hackers distribute malware. To name just a few, our Text Scam Detector blocks links to suspicious sites that host malware and other attacks — and our Web Protection does the same for your browser. It also includes our industry-first online protection score that shows you just how safe you are, along with suggestions that can make you safer still. Together, our McAfee+ plans offer more than just antivirus. They protect your devices, your privacy, and your identity overall.
[i] https://www.historyofinformation.com/detail.php?entryid=2860
[ii] https://www.historyofinformation.com/detail.php?id=1676
[iii] https://www.theatlantic.com/technology/archive/2016/05/the-computer-virus-that-haunted-early-aids-researchers/481965/
[iv] https://www.forbes.com/sites/daveywinder/2020/05/04/this-20-year-old-virus-infected-50-million-windows-computers-in-10-days-why-the-iloveyou-pandemic-matters-in-2020