October is finally among us, and things are spookier than usual. One ghost causing some hocus pocus across the World Wide Web is Ghostcat-3PC, a browser-hijacking malware that has launched at least 18 different malvertising campaigns in the last three months. According to SC Magazine, Ghostcat’s goal is to hijack users’ mobile browsing sessions and is specifically targeting website visitors in the U.S. and Europe.
How exactly does this ghost begin its haunting? The infection begins when a user visits a particular website and is served a malicious advertisement. When this occurs, Ghostcat fingerprints the browser, which is when information is collected about a device for the purpose of identification, to determine if the ad is running on a genuine webpage. Ghostcat also checks if the ad is running on one of the over 100 online publishers’ pages that have been specifically targeted by this campaign. If both of these conditions are met, then the malware serves a malicious URL linked to the ad.

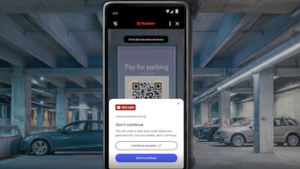
From there, this malicious URL delivers obfuscated JavaScript, which creates an obscure source or machine code. The attackers behind Ghostcat use this technique to trick the publishers’ ad blockers, preventing them from detecting malicious content. The code also checks for additional conditions necessary for the attack. These conditions include ensuring that the malware is being run on a mobile device and a mobile-specific browser, that the device is located in a targeted country, and that it is being run on a genuine website as opposed to a testing environment. If the malware concludes that the browsing environment fits the descriptions of their target, then it will serve a fraudulent pop-up, leading the user to malicious content.
Tips to Avoid Malware
So, what are some proactive steps users can take to avoid being haunted by Ghostcat? Follow these tips to avoid the malware’s hocus pocus:
- Watch what you click. Avoid clicking on unknown links or suspicious pop-ups, especially those that come from someone you don’t know.
- Be selective about which sites you visit. Only use well-known and trusted sites. One way to determine if a site is potentially malicious is by checking its URL. If the URL address contains multiple grammar or spelling errors and suspicious characters, avoid interacting with the site altogether.
- Surf the web safely. You can use a tool like McAfee WebAdvisor, which will flag any sites that may be malicious without your knowing.
And, of course, to stay on top of the latest consumer and mobile security threats, be sure to follow @McAfee_Home on Twitter, listen to our podcast Hackable? and ‘Like’ us on Facebook.